How to Block an IP Address with iptables: A Complete Linux Guide

When doing business online, you will inevitably have to deal with abusive users spamming or clogging your blog’s comments, flooding your server with requests, or harassing your users.
The good news is you can quickly deal with them using Linux iptables, to block IP addresses immediately!
At ServerMania, we stands proud as an authority in server management, empowering webmasters to secure their system against threats targeting IP addresses.
While our Cloud Servers and Linux Dedicated Server Hosting Solutions are secure in their core, knowing how to manage IP addresses efficiently, ensures your workload’s safety.
So, whether you’re blocking a rogue script or fine-tuning your iptables, ServerMania’s got your back with this in-depth guide, walking you through the process.
Why Block an IP Address on Linux Server?
In 2025, your Linux server is a magnet for abusers such as bots, spammers, or worse. Blocking an IP address with iptables answers the need to define a secure boundary against intruders.
Here are the main reasons why you would ever need to block an IP addresses:
- Disarm Spammers: Spammers flooding your blog’s comments surely deserve a harsh block.
- Halt Bot Attacks: Bots flooding your server with requests needs to be dealt with immediately.
- User Experience: IPs (abusers) that are harassing your readers/visitors cannot be tolerated.
- Stop DDoS Attack: A flood of malicious traffic from one IP, (DDoS), deserves instant block.
Blocking and IP address is not as daunting as it sounds. With just a few commands, you’ll block IP and get back to your operations with a piece of mind.
You’ll only need a root access, so log into your server (via console or secure connection), and let’s walk you through the commands you’ll use to block an IP address.
Read Also: What is IP Transit? Service and Pricing Guide
How to Install iptables in Ubuntu?
Most Ubuntu versions come with iptables pre-installed, but if it’s missing or you’re setting up a fresh server, that command will get it installed:
sudo apt-get install iptablesHow to Block IP Addresses, IP Range & Subnet
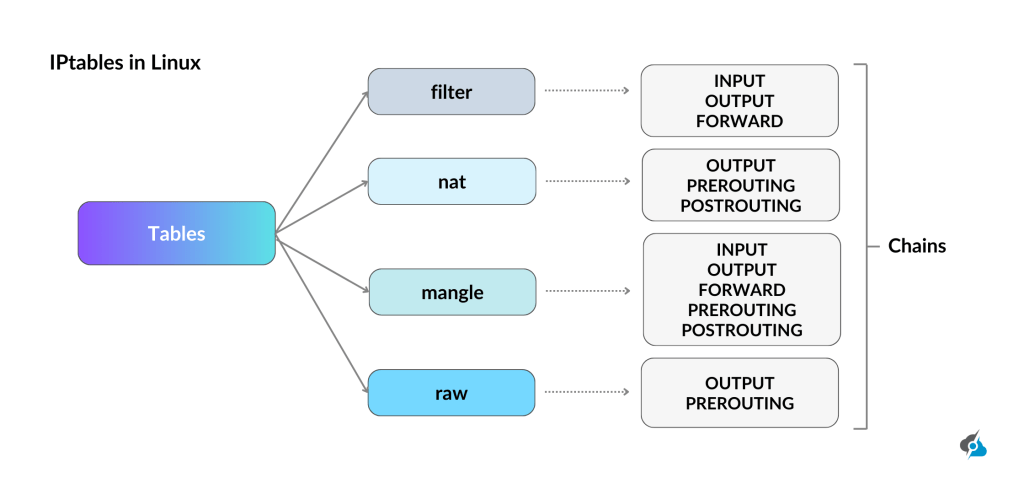
So, if you’re ready to deal with the troublemakers off your Linux server, we are going to introduce how iptables firewall work and how to block IP addresses immediately.
We’ll guide you through the commands to link and block a specific IP, an IP range, or a complete subnet on your Ubuntu system assuming you’re logged in with root access. Let’s get to it!
Blocking Specific IP Address:
If you have a single IP address causing you trouble, like a abusive spammer, the following command will permanently block their IP address:
iptables -A INPUT -s [IP] -j DROPJust replace [IP] with the target address (e.g., 192.168.1.100).
Blocking Specific IP Range:
Sometimes, multiple IP addresses, like a botnet, may try to output malicious traffic to mess your server.
So, the following iptables command blocks them all at once:
iptables -A INPUT -m iprange --src-range [START]-[END] -j DROPSwap [START] and [END] with the range endpoints (e.g., 192.168.1.100-192.168.1.200):
Blocking Complete Subnet:
When you have to deal with a complete subnet, for instance a rogue network flooding your website, the following command can easily block them all at once:
iptables -A INPUT -m iprange --src-range [START]-[END] -j DROPJust replace [SUBNET ADDRESS] with the subnet and verify eth1 matches your interface.
Blocking an Interface Connection:
If you’re wondering how to block a connection through a specific interface use the following command:
iptables -A INPUT -i [Interface Name] -s [IP] -j DROPFeel free to include a “+” sign to the end of the interface name, so you can block any interface with a name that begins with the characters you’ve inserted.
How to Block a Specific Port?
As a webmaster, blocking one IP address or an IP range may not resolve all your issues and sometimes you need to shut down a specific port. This may be especially helpful when a spam bot is sneaking to your mail server on a specific port, or an abusive script is causing you trouble.
In 2025, with servers under constant cyber attacks, iptables firewall allows you safeguard your ports, locking out connections to any specific one.
Use the following command to block a connection on a specific port:
iptables -A INPUT -s 65.55.44.100 -p tcp --destination-port 25 -j DROPThis command prompts iptables to drop all TCP traffic from the specified IP affecting port 25. The -p tcp flag targets TCP protocol (swap for udp if needed), and -j DROP ensures the packets would vanish.
Make sure to run this with root access via your server’s router console to block the port forwarding.

How to Block Specific Country or Region
By mapping IP addresses to geographic locations, you can filter out unwanted visitors while keeping your Linux operating system secure.
Let’s explore using GeoIP with iptables, installing its modules, setting country-specific rules, and weighing performance impacts.
Using GeoIP Databases with iptables
GeoIP databases link IP addresses to countries, enabling iptables to block traffic by specific regions. The Firewall uses the xt_geoip module to match these locations, perfect for targeting bot countries.
iptables -m geoip --src-cc [COUNTRY_CODE] -j DROPExample Country Blocking Rules
Block traffic from specific countries (e.g., China, CN) or allow only one (e.g., US) with these rules.
Replace country codes as needed for your system’s needs.
iptables -I INPUT -m geoip --src-cc CN -j DROPiptables -I INPUT -m geoip ! --src-cc US -j DROPHow to View Blocked IP Addresses
If you’ve been restricting IP addresses, ranges and subnets, and now you’re wondering how to check the list of all abusers, use iptables firewall or UFW status to peek at your blocklist.
Whether you’re troubleshooting or just curious to explore blocked IP addresses, run either of the following commands to inspect the blocklist:
iptables -L -v/sbin/iptables -L INPUT -vsudo ufw statusThe -L flag lists all rules, while -v adds details like packet counts and source IP addresses. For example, iptables -L -v shows every IP you have blocked with a DROP rule. The second command, is mainly used to focus on incoming traffic rules if your setup is quite complex.
How to Search for a Blocked Address
If you need to search for specific IP you’ve blocked in the past, iptables allows you search through the blocklist easily. So, the following syntax can help you confirm if an IP’s blocked out, saving you from scrolling through the endless rules:
iptables -L INPUT -v -n | grep [IP]Just, replace [IP] with the address you’re checking (e.g., 192.168.1.100).
How to Remove Blocked IP Addresses
Sometimes you may need to unblock a specific IP address to restore its output flow, especially when it was blocked by mistake. Luckily, iptables on Ubuntu allows you to undo your blocks as easily as you set them. Whether you’re clearing a specific IP or tweaking the blocklist, a few commands can make it easy.
To remove a blocked IP, first check your blocklist with line numbers, delete the specific rule, and verify the change. Then, run these commands in order, replacing [LINE] with the rule’s line number (e.g., 3):
iptables -L INPUT -n --line-numbersiptables -D INPUT [LINE]iptables -L INPUT -v -nIf you know the exact IP to unblock (e.g., 1.2.3.4), this single command does the trick:
iptables -D INPUT -s 1.2.3.4 -j DROPAlso, if you want to log dropped packets for insights, this command logs attempts from an IP or subnet, replacing [IP/SUBNET] with the target (e.g., 192.168.1.0/24) and verifying eth1 matches your interface:
iptables -i eth1 -A INPUT -s [IP/SUBNET] -j LOG –log-prefix “IP DROP SPOOF A:”
How to Save Changes to Blocklist
When you’re ready with dealing with abusers, unblocking or making other tweaks, you need to save the changes you’ve made to your iptables firewall rules on CentOS, RHEL, or Fedora.
Use the following command to save all changes:
iptables saveThis command saves all your iptables rules to the configuration system, keeping network infrastructure secure. Run it with root access in your terminal, and you’re set.

Additional Commands To Block An IP Addresses:
Now that you’ve got the basics of IP blocking with iptables firewall, sometimes you need to tighten the security measures even further.
The core commands are a solid start, but with bots and hackers getting smarter, you’ll want a few extra commands ready to shut down any IP address causing you trouble.
Block Outgoing Data (OUTPUT)
If you want to prevent data leaks outgoing from your server, the following command stops outgoing traffic connections from a specific IP instantly:
iptables -A OUTPUT -s [IP] -j DROPBlock Forwarded Data (FORWARD)
If an IP is using your server as a pass-through for malicious flow, the following command is perfect against proxy abusers:
iptables -A FORWARD -s [IP] -j DROPBlock TCP Connections (TCP)
When a spammer is abusing a specific service, like your mail port, this iptables command cuts their TCP connection in seconds:
iptables -A INPUT -p tcp -s [IP] -j DROPBlock Port Probing (ICMP)
Any hackers pinging your server to locate weaknesses, can be neutralized immediately, by using this iptables command to blocks their ICMP probes:
iptables -A INPUT -p icmp -s [IP] -j DROPWith these commands in your toolkit, you’re ready to safeguard your local network, from spammers to snoopers, keeping your server untouchable.
How to Build Your iptables Block List?
Now that you know how to deal with abusive IP addresses, it’s time to build your blacklist to keep your Linux server safe from the digital threats.
With iptables, you can start fresh, lock down your server, and block troublemakers with precision. The process involves clearing old rules, setting strict defaults, and adding your blocks. Here’s how to build a block list, assuming you’re logged in with root access on your server’s terminal:
Flush Old Rules
Before you start, wipe out any outdated or default rules cluttering your setup. The following command resets iptables to a clean slate, ready for your custom list.
iptables -FSet Chain Policies
Now, enhance your server by setting strict default policies to drop all flow unless you say otherwise. These commands lock down incoming, forwarded, and outgoing connections by default.
iptables -P INPUT DROPiptables -P FORWARD DROPiptables -P OUTPUT DROPIP Blocking Rules
With the slate clean and defaults values, it’s time to add your specific blocks. Use the IP blocking commands from earlier sections to target spammers, bots, or other nuisances.
iptables -A INPUT -s [IP] -j DROPYour block list is now live, turning your server into a no-go zone for unwanted IPs. Tweak as needed to keep your network infrastructure secure and running.
Simplifying Security with Uncomplicated Firewall (UFW)
If iptables firewall seems too manual work for you, meet the Uncomplicated Firewall (UFW), which is your Linux operating system best friend against cyber threats.
In 2025, with spammers and bots getting smarter, UFW simplifies blocking IP addresses or tweaking ports on Ubuntu or Debian operating systems.
Here are some examples to consider:
Block an IP Address via UFW
If you need to prevent bot from entering your server via UFW, the following command blocks all data flow from a specific IP address, similarly as iptables rules:
sudo ufw deny from [IP]Allowing Server Port via UFW
If you want to keep your SSH port open for legit users only using UFW, the following command allows network load to a chosen port, like 22 for SSH, without exposing others.
sudo ufw allow [PORT]/tcpBlocking a Server Port via UFW
If you have a spammer clogging your mail port, the following command for UFW shuts down packets flow to a server port, from any source, so use the following syntax:
sudo ufw deny [PORT]/tcpThese UFW commands make securing your server easy, so it’s good to have a grasp of how they work.

Read Also: What Is IP Restriction and How Does It Work?
Block IP Addresses iptables – FAQ
Will my iptables rules survive a system reboot?
No, unless you save them with (iptables-save) on CentOS, RHEL, or Fedora to verify your rules are saved post server reboot.
How can I block all IPs except a whitelist?
Set a default DROP policy (iptables -P INPUT DROP) and allow IP addresses with iptables -A INPUT -s [IP] -j ACCEPT.
What’s the difference between DROP and REJECT targets?
DROP silently discards IP address forwarding traffic, while REJECT sends an error response, potentially alerting the sender.
How do I block an entire country?
Use GeoIP modules with iptables to block country-related IP addresses ranges, requiring additional setup like xt_geoip.
Can iptables block DDoS attacks effectively?
Iptables can mitigate small DDoS attacks by IP blocking or limiting connections, but large attacks need advanced tools.
How do I see which IPs are currently blocked?
Run iptables -L -v to view all blocked IP addresses and rules in your iptables configuration.
Is there a limit to how many IPs I can block?
There’s no strict limit, but too many rules can slow your server, so optimize with ranges or subnets.
How do iptables and Docker interact?
Docker manages its own iptables rules, which can conflict; use Docker’s –iptables=false flag for manual control.
Should I use iptables or nftables on new systems?
nftables is the newer, more flexible choice for modern systems, but iptables is still reliable for existing setups.
ServerMania’s IP Transit Leasing service offers a smart way to keep abusers away! Talk to an expert now and get started today.
Was this page helpful?

